Security experts claim that most of the payment terminals, also known as PoS Payment Systems, used in Germany, contain old vulnerable protocols, but also use bad practices when it comes to encrypting data.
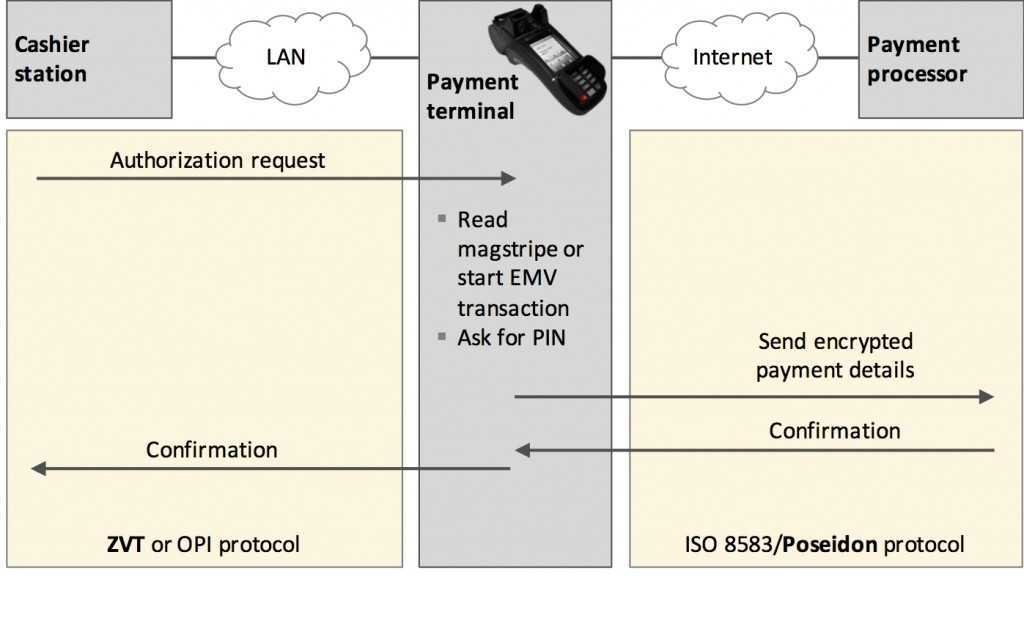
According to the researchers, the problem exists in both communication processes, ie protocol που usestai to contact the PoS Payment a cashier device with the store station, and the protocol that sends the data from the payment terminal to the bank for processing the data.
Vulnerable inside…
On the local communication side, the researchers found that a high percentage of German payment processors use the ZVT protocol, which is known to be susceptible to simple eavesdropping attacks and which allows a hacker to intercept credit card information. cards.
What makes things worse is that this protocol is also responsible for reading the PIN of the card via PoS and sending it back to the central station to allow the transaction.
Although this communication is encrypted, researchers found that PoS (Point of Sale) manufacturers store the encryption key on the device, and often use the same key.
… Vulnerable abroad
Between the PoS terminal and the bank, things are not so rosy. The protocol used to exchange data between these two, a variant of the ISO 8583 standard known as Poseidon, has a flaw control identity.
By repeating the same error, PoS manufacturers also store the encryption key used to exchange encrypted data with third parties. This key is stored on the device itself and rarely changes, most of the time is the same for whole lots of PoS terminals.
Researchers are scheduled to make an extensive presentation on this topic on Sunday at 27 December in Hamburg at the 32 Chaos Communications Conference (32C3).