The following post is for everyone who is anxiously awaiting the Windows 10 Anniversary Update. The company is expected to release the much-anticipated update today, but it is not thinking about securing its system that offers a serious security gap to malicious users since 1997.

A flaw in the way Windows handles old shared network resources (shared network resources) can leak Microsoft user account, password accesss or VPN, if the victim uses a VPN to surf the Internet.
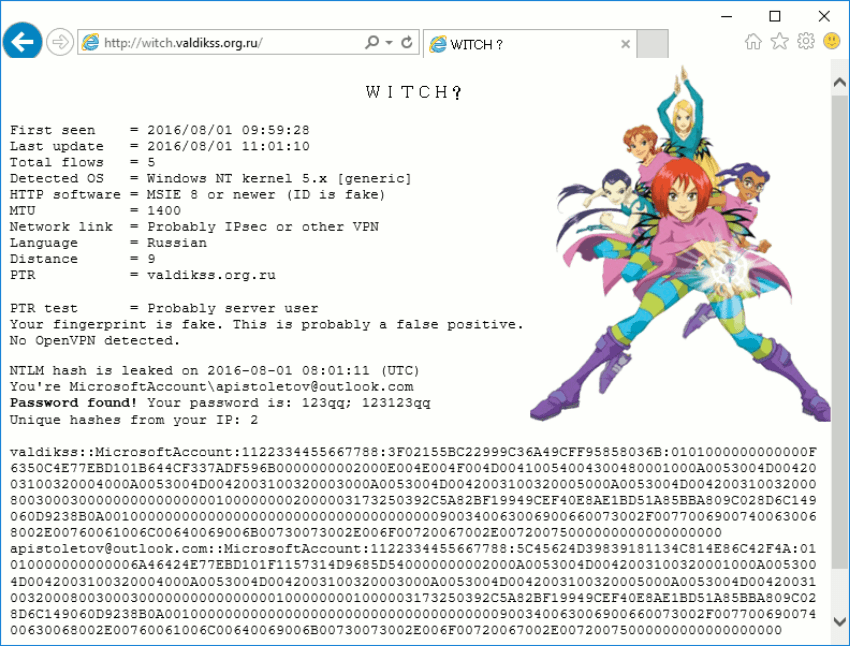
The exploit allows an attacker to integrate a link to a SMB resource (network share) within a web page or e-mail to be viewed through Edge, Internet Explorer or Outlook respectively.
The attacker can mask the connection to the network share he uses in image tags, and instead of the correct link to the image, he can place a link to a shared network component hosted on his own network.
When a user opens this link through Internet Explorer, Edge, or Outlook, because of the way Windows manages the control ID cards on shared networks, their computer will automatically send their login credentials for authentication to the scammer's computer.
The Microsoft account password does not run in plain text, but with NTLM hash. Researchers have long proved that these hashes can easily break.
The issue we described above is not new and not just Windows 10. Microsoft and the research community are aware of this issue from 1997 and are often discussed at security conferences, such as Black Hat.
But what has changed since Windows 8 is that Microsoft has begun to allow users to authenticate to their computers with Microsoft accounts.
In Windows 10, this has become the de facto method for authentication, which means that more users have started using it.
In recent years, Microsoft has begun to connect all of its online services with the user's Microsoft account.
Thus, according to ProstoVPN's ValdikSS, this old attack allows fraudsters to obtain the credentials of Microsoft accounts that grant indirect access to all of the company's services: Windows 10, Skype, Xbox, OneDrive, Office 360, MSN, Bing, Azure, and many others.
ValdikSS states that the easiest way to protect yourself from these types of attacks is to block all outgoing SMB connections (door 445) through the Windows firewall, except on local networks.





