Your browser may store sensitive data, including usernames, passwords, and session cookies, in plain text in memory. Check how yours behaves.
According to CyberArk security researcher Zeev Ben Porat, most programs browsing web based on Chromium, including the famous Chrome seem to be affected by this programmability.
But he's not the only one. And the Microsoft Edge and Brave are susceptible, and even Mozilla's Firefox web browser is also affected by the problem.
Which is the subject; That your browser caches all your sensitive data in clear text and not encrypted. To view saved passwords and names is not required physics presence on the target machine, nor administrator rights, as remote access or even running a software malware on the target machine is sufficient to extract the data.
Two-factor authentication security may not even be enough to protect user accounts if there is cookie data in memory.
Security researcher Zeev Ben Porat describes many different types of credential data in text form that can be extracted from the browser's memory. Such as:
- Username + password used when logging in to a targeted web application
- URL + Username + Password are automatically loaded into memory when the browser is started by password management
- All URL + username + password entries stored in login data
- All cookies that belong to a specific web application (including session cookies)
Το πρόβλημα αναφέρθηκε στην Google και η απάντηση που έλαβε ήταν ότι "δεν θα επιδιορθωθεί". Ο λόγος που δόθηκε είναι, ότι το Chromium δεν θα διορθώσει προβλήματα που σχετίζονται με επιθέσεις φυσικής τοπικής πρόσβασης.
Try your own browser
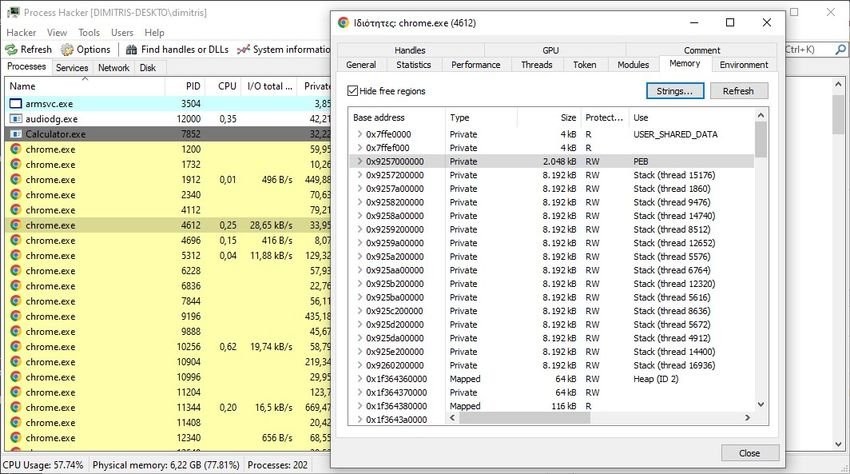
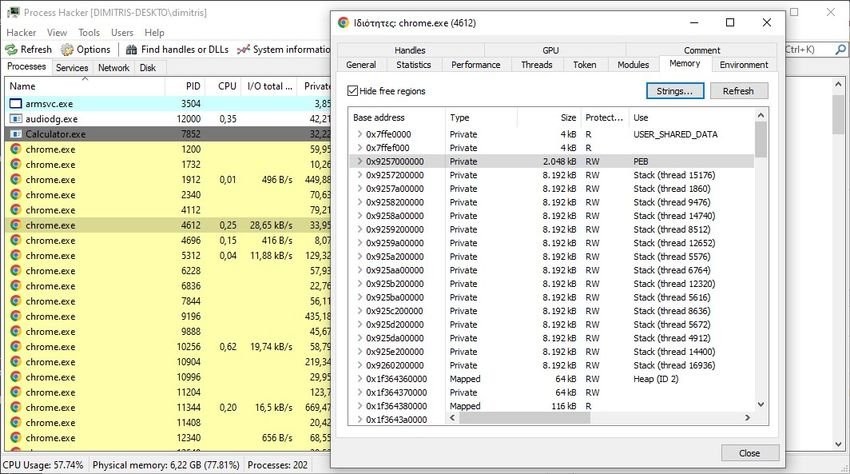
Windows users can use free Process Hacker tool to test their browsers.
Simply download the portable version of the program, extract the zip archive of and run the file Processhacker.exe to get started. Then do the following test:
Step 1: Enter a username, password, or other sensitive data on a random page in the browser you want to try.
Step 2: Double-click the main browser process in the Process Hacker process list for details.
Step 3: Go to the Memory tab.
Step 4: Activate the Strings button on the page.
Step 5: Click OK on the page.
Step 6: Ενεργοποιήστε το κουμπί Filter (Φίλτρο) στο παράθυρο που ανοίγει και επιλέξτε το "Contains" (περιέχει) από το μενού περιβάλλοντος.
Step 7: Πληκτρολογήστε τον κωδικό πρόσβασης του βήματος 1 ή άλλες ευαίσθητες πληροφορίες στο πεδίο "Enter the filter pattern" (Εισαγάγετε το μοτίβο φίλτρου) και επιλέξτε ok.
Process Hacker will return your data if it is found in process memory.





