Comodo Antivirus security software contains many vulnerabilities that could put users at risk, according to Tenable Research researchers.
Tenable Research reports that the 12.0.0.6810 version of Comodo Antivirus and Comodo Antivirus Advanced contains multiple vulnerabilities.
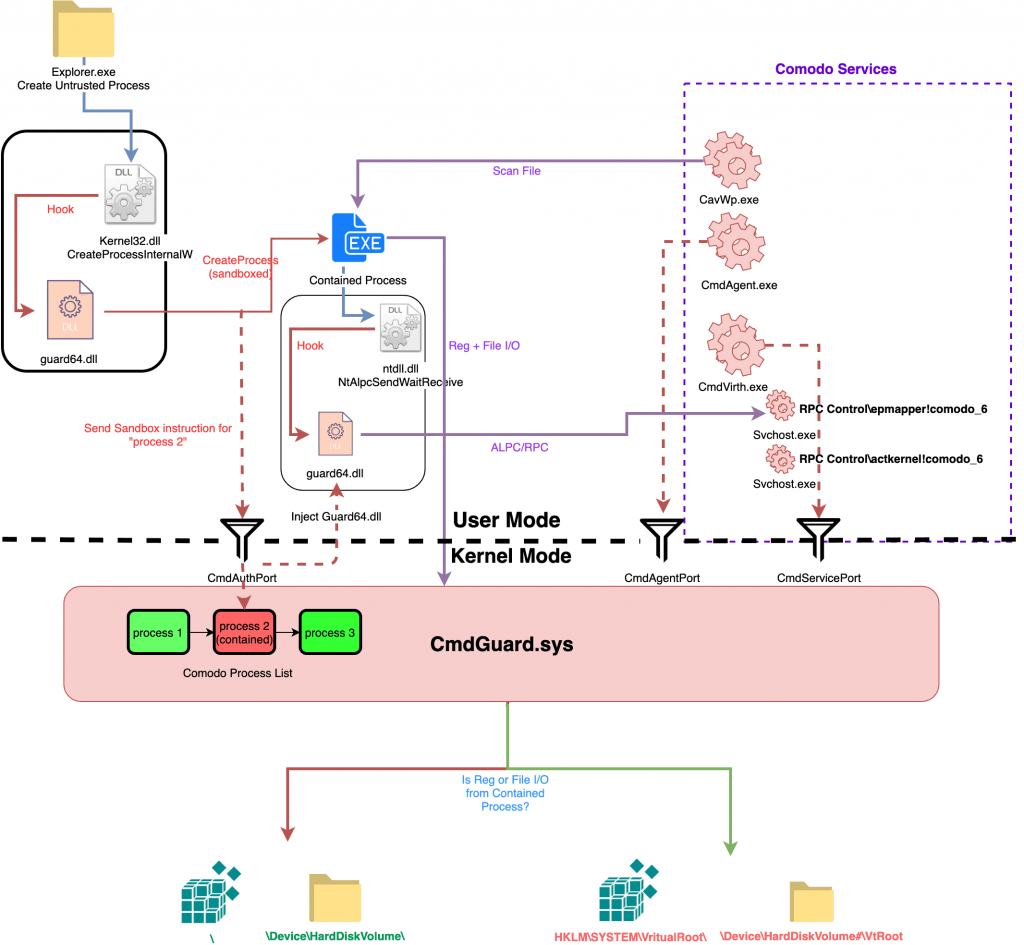
David Wells carried out an in-depth check on these vulnerabilities and in a post to Medium blog, describes how security holes could be used to allow a malicious user to escape from sandbox and gain system-level rights. The researcher also published a PoC.
The first vulnerability, CVE-2019-3969, is a software issue in CmdAgent that allows attackers to bypass legitimate signature checks. Attackers are able to gain rights at the system level.
The second bug is CVE-2019-3970, and it appears to be a very serious one problem in handling the Comodo software database. Tenable states that the database can be stored in a protected folder on disk, but it is possible for any low-privilege process to modify the files in memory.
Another security gap is CVE-2019-3971, caused by an LCP port, cmdvrtLPCServerPort ..
Another is CVE-2019-3972, and is available at CmdAgent.exe.
The researcher also mentioned CVE-2019-3973, which affects security software only until the 11.0.0.6582 version.
Tenable's findings were shared with Comodo on April 17. By June, some of these were confirmed, with the LPE bug according to Comodo “due in part to an error by Microsoft. "
We are currently awaiting fixes from the security company. If you use any of the applications that we mentioned above, it would be good to use another, reliable one.
_________________
- Hack Right EU plan to convert black to white hat hackers
- VLC: Doubts the existence of a security vacuum
- SmartScreen disable on Windows Edge 10 1903
- Equifax 20.000 to every person who leaked his data
- Huawei: White House & Technology Companies Discuss Foreclosure
- Windows 10 May 2019 Update ISO with all the latest patches





