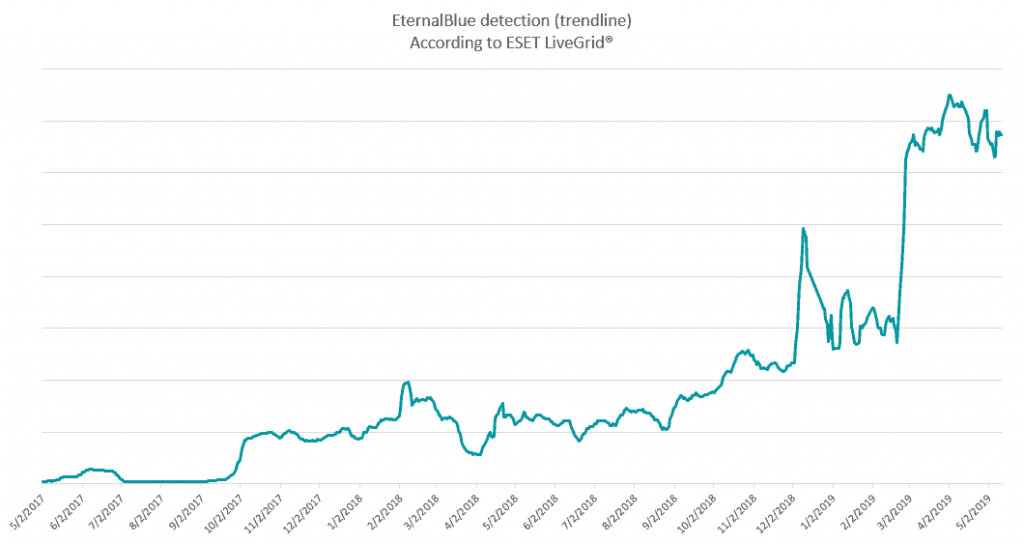
According to her telemetry ESET, attacks based on exploit EternalBlue έχουν αγγίξει ιστορικά υψηλά επίπεδα, με τους users to be bombarded with hundreds of thousands of attacks every day.
It has been two years since the exploit EternalBlue opened the door to one of the most violent cyber attacks in history, known as WannaCryptor (or WannaCry).
Since then, attempts to abuse the specific vulnerability have been greatly increased by the particular exploit, and are currently at their peak, as ESET researchers report.
The EternalBlue exploit was reportedly stolen by the NSA on 2016 and released on April 14 by a group of cybercriminals known as Shadow Brokers. The exploit targets a vulnerability in the implementation of the SMB (Server Message Block) protocol via the 2017 port.
Although Microsoft had released a patch, and even before the launch of WannaCryptor 2017, there are still vulnerable systems around the world today, possibly due to inadequate security practices and patch updates.
EternalBlue is responsible for many cyber-attacks, such as Diskcoder.C (also known as Petya, NotPetya and ExPetya) and BadRabbit in 2017. Also, well-known cybercriminals such as the Sednit group (aka APT28, Fancy Bear and Sofacy) have used it to attack hotel Wi-Fi networks. Recently, EternalBlue has been held responsible for the spread of Trojans and malware miningof cryptocurrencies in China.
According to ESET researchers, this exploit and all cyberattacks highlight the importance of timely patching. Furthermore, they highlight the need for a reliable and polyflat security solution that can do much more than just stop the transfer of the malicious payload, such as protect against the underlying mechanism.
______________________
- Anonymous: the end of hacking
- Microsoft, Sony collaboration for game-streaming
- Google Chrome Canary: new configuration page





