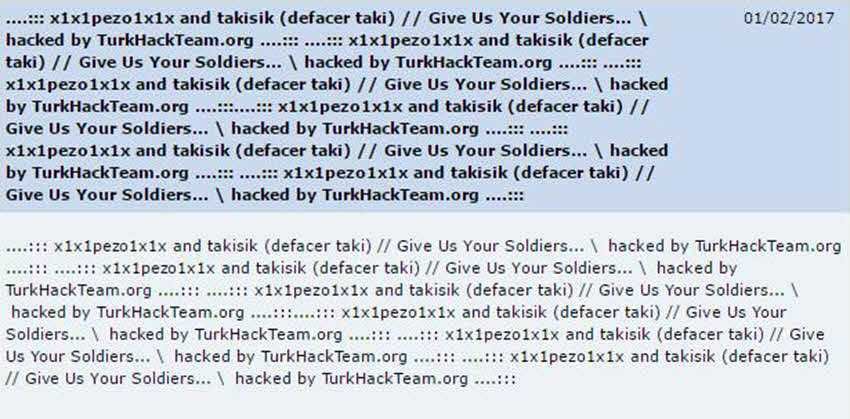
The Department of Physics of the University of Patras fell victim to attack by Turkish hackers who had the opportunity to request in their own way the extradition of 8 Turkish soldiers who came to Greece immediately after the coup against Recep Tayyip Erdoğan's government.
So on Wednesday February 1, the official websiteσελίδα του Τμήματος Φυσικής του Πανεπιστημίου Πατρών βρέθηκε παραμορφωμένη με το ανορθόγραφο μήνυμα των Τούρκων hackers οι οποίοι απαιτούσαν να τους επιστρέψουμε τους "στρατιώτες μας."
And the whole page:
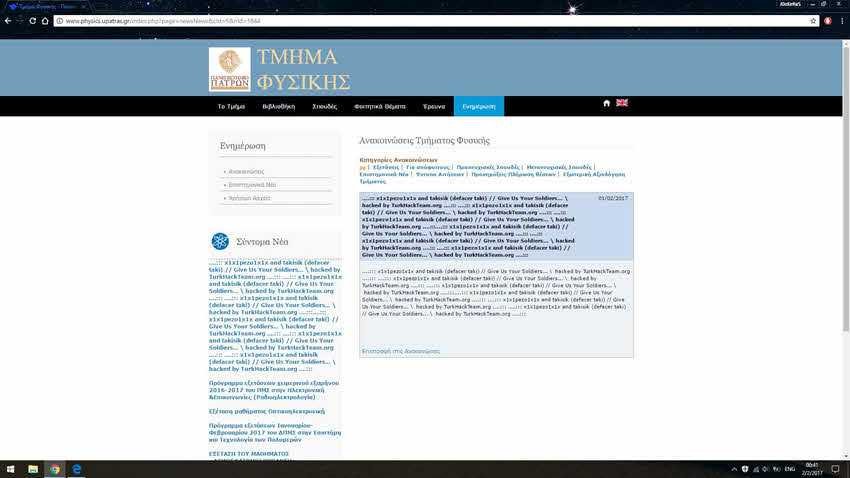
It should be mentioned that if you look at the page of the University of Patras today, it has returned to its original form and it is as if there was no previous attack. But according to a complaint we received from our reader (Nyo/GHS) n vulnerability that allowed the Turks to post their message is still open, i.e. not fixed.
To prove this, the researcher sent us a screenshot that is distinguished that he has been linked to the site with the University Secretariat account. So as you can see if the vulnerability still exists, anyone can use it.
The security gap may not give full access to the site or the server as University technicians have added some filters, but it is just as serious because it allows a malicious or non-malicious user to add code in html or javascript format and to influence everyone who enters on the site. Of course with javascript they can deform the whole page (Post Reflected Deface).
Let us mention that the link that leads to the vulnerability is available για όλους και βρίσκεται στο footer σελίδας. Το χρησιμοποιούν μέλη αλλά και η ομάδα διαχείρισης της ιστοσελίδας. Η επίθεση που έγινε από αυτό το σημείο, ήταν μια πολύ απλή μορφή SQL injection (SQLi).
With a very simple SQLi query, Nyo managed to overtake the login form and get into the site. From the management panel, you could make posts, upload files, and more, as you'll see below: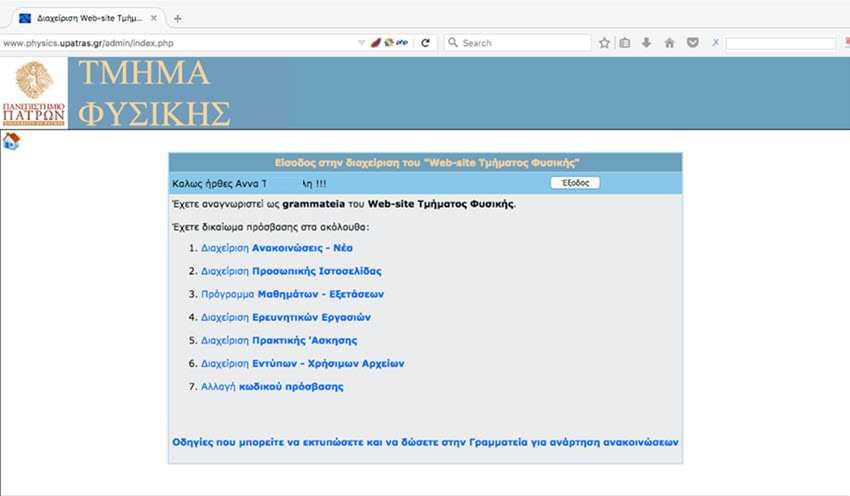
Meanwhile, it is worth mentioning that the SQLi query used by Nyo was very simple and the researcher pointed out that it could affect the site's publications with Persistent XSS.
By the same method it could affect both admin and visitors to the page, by changing pages and posts and adding malicious scripts.
It should be noted that we still have the impression that such a security gap still exists, leaving exposed page data but also a manager to its visitors.
Nyo even told us that the gap is not new, that there is a long time ago and that the page has been hacked by hackers who used exactly the same SQLi.
Let's hope that this time it will be repaired, before anyone else begins to take on how effective a hacker is, on a page that no one fixes.
SecNews.gr remains at the disposal of any interested administrator who wants to fix the vulnerability.





