Attackers need a little more than a minute to gain access on Linux systems by holding down the Enter key for exactly 70 seconds. This particular "hack" gives them a root initramfs shell as a gift.
Simple exploit exists because of a bug in the Linux Unified Key Setup (LUKS) used by popular Linux distributions.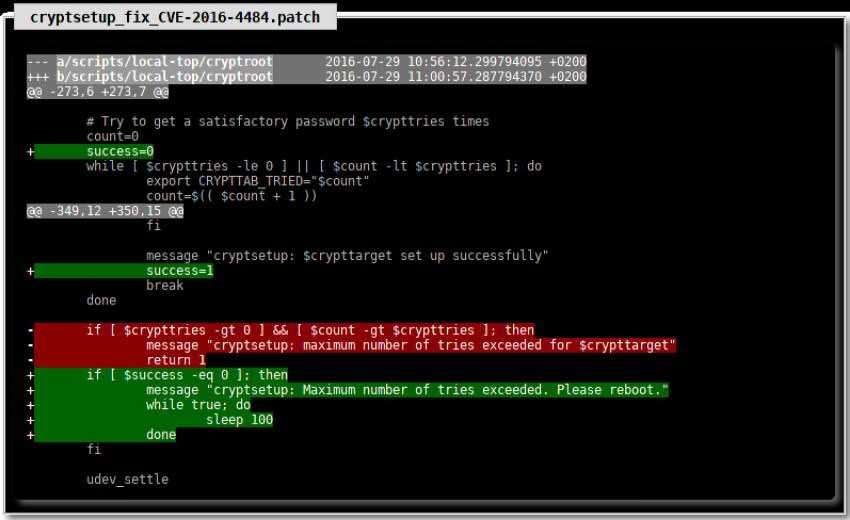
Let's say that with shell access, an attacker could decrypt systems. The attack also works on Linux cloud systems.
Debian and Fedora are two distributions that have been confirmed to be vulnerable to the problem.
The problem was identified by Hector Marco, a lecturer at University West of Scotland, along with assistant professor Ismael Ripoll from the Polytechnic University of Valencia. Researchers say the problem does not require a particular configuration of the system and they say:
This vulnerability allows [the hacker] to obtain a root initramfs shell on the affected systems. The vulnerability is highly reliable because it does not depend on specific systems or configurations.
Attackers can copy, modify or destroy the hard drive, as well as create a network to extract the data. The vulnerability is particularly serious in environments such as libraries, ATMs, airport machines, laboratories, etc., where for the entire boot process the protection is in the BIOS password and GRUB and they only have a keyboard or even a mouse.
The exploit has been repaired according to Marco and Ripoll.
http://hmarco.org/bugs/CVE-2016-4484/CVE-2016-4484_cryptsetup_initrd_shell.html





