North Korea's government hacking group Lazarus has added another tool to its arsenal. This time it is a Windows Update client that uses the technique living-off-the-land binaries (LoLBins) to run malicious code on Windows systems.
Η νέα μέθοδος ανάπτυξης κακόβουλου λογισμικού ανακαλύφθηκε από την ομάδα Malwarebytes Threat Intelligence κατά την ανάλυση μιας εκστρατείας spearphishing τον Ιανουάριο που υποστήριζε ότι ήταν η αμερικανική εταιρεία ασφάλειας και αεροδιαστημικής Lockheed Martin.
If victims open the maliciously attached Word documents and trigger macro execution, a macro drops a WindowsUpdateConf.lnk file into the startup folder and a DLL file (wuaueng.dll) into a secret Windows/System32 folder.
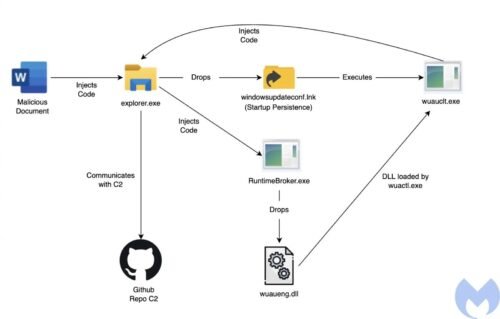
In the next step, the LNK file is used to launch the WSUS / Windows Update client (wuauclt.exe) which runs another command to load the malicious DLL of attackers.
"It's an interesting technique used by Lazarus to run its malicious DLL using the Windows Update Client and bypass security detection mechanisms." he says Malwarebytes.
The researchers linked these attacks to the Lazarus team based on a number of factors, including overlaps in their infrastructure, metadata of documents, and similar targeting of previous campaigns.
This tactic was discovered by MDSec researcher David Middlehurst, who found that intruders could use a Windows Update client to run malicious code on Windows 10 systems.
This can be done by loading a specially crafted DLL and using the following command line (the command used by Lazarus to load the malicious load of):
wuauclt.exe / UpdateDeploymentProvider [path_to_dll] / RunHandlerComServer
MITER ATT & CK reports that the attack uses a way of defensive avoidance strategy known as Signed Binary Proxy Execution and allows attackers to bypass it security software, application control and digital certificate validation protection, since everything is done through Windows Update.
The Lazarus group (also known as HIDDEN COBRA by US intelligence services) is a North Korean military hacking group that has been active for more than a decade, at least since 2009.





