In the first part of the “Network Basics” series, I have introduced you to the basics of networks, including IP addresses, ports, NAT and DHCP.

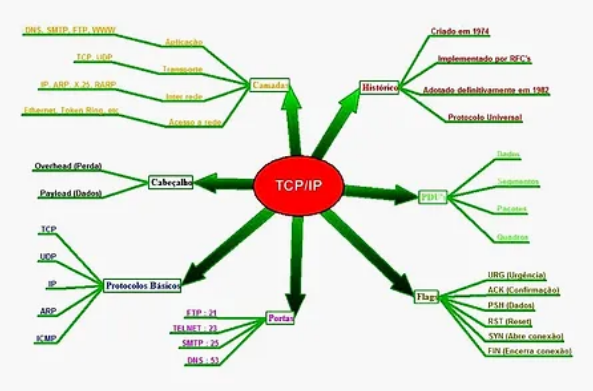
In this second part, I will introduce you to the basics of TCP/IP, namely Transmission Control Protocol (TCP) and Internet Protocol (IP). These are the most common protocols used on the internet for communication.
To become an expert in networks, you should understand the structure and anatomy of these protocols. In my experience, many professionals in these fields do not understand the basics of TCP/IP, which means that you will definitely have an advantage over them if you understand TCP/IP.
When trying to build a new hacking tool or investigate an attack on a network, understanding these protocols and their fields is essential. Otherwise, you'll just be wasting your time.
What are protocols?
Protocols are just a way to communicate. For example, we here at iguru have agreed to write articles in the Greek language with all its rules and grammar as a way of communication. This is our protocol. If we didn't have an agreed upon way of communicating, people would use multiple languages, grammars and rules and none of us would understand each other.
The protocols are similar. A protocol simply defines a way of communication with all its rules. These rules are usually defined by an RFC (Request for Comments).
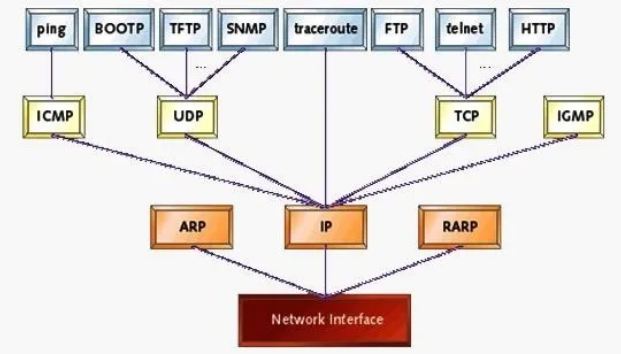
There are many protocols used on the internet. These include TCP, IP, UDP, FTP, HTTP, SMTP, etc. and each has its own set of rules that must be followed in order to communicate effectively (similar to the rules we use in texting).
Probably the two most important protocols for use on the internet are IP and TCP, so let's take a look at each of them.
IP (Internet Protocol)
IP or Internet Protocol is the protocol used to define it addressς IP της πηγής και προορισμού ενός packetuh, as this crosses the internet. It is often used in conjunction with other protocols such as TCP, hence the commonly used combination TCP/IP.
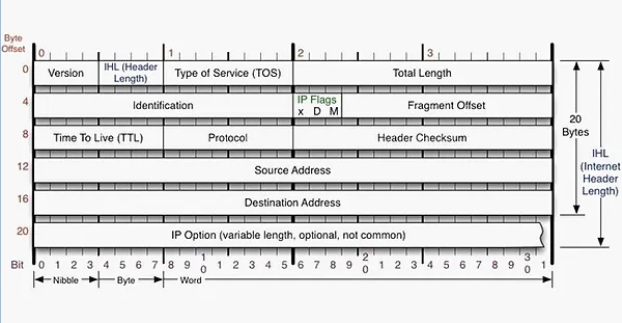
Let's take a look at the header of an IP packet and see what information it contains that may be useful to the would-be hacker and/or security researcher.
Row NEVER
-
Specifies the IP version, either v4 or v6.
-
IHL: Specifies the length of the header.
-
Type of Service (TOS): Specifies the service type of this package. These include minimizing latency, maximizing throughput, maximizing reliability, and minimizing monetary cost.
-
Total Length: Specifies the total length of the IP datagram (including data) or fragment. Its maximum value is 65.535.
row2
-
Login: This field uniquely identifies each packet. It can be critical for reassembling fragmented packets.
-
IP Flags: This field specifies whether the packet is fragmented (M) or not (D). Field manipulation can be used to evade IDS and firewalls. It can also be used in conjunction with the Window field to specify the operating system of the sender.
-
Fragment Offset: This field is used when packets are fragmented. Specifies where packets should be reassembled from the beginning of the IP header.
Row NEVER
-
TTL: This determines how many trips across the internet the packet will take before it expires. It varies by operating system, which makes it useful to determine the operating system of the sender.
-
Protocol: This field specifies which protocol is used with the IP. Most of the time, it is 6 for TCP, 1 for ICMP, 17 for UDP, among others.
-
Header Checksums: This is an error checking field. Computes the checksum (a simple algorithm) to determine the integrity of the data in the header.
Rows 4 & 5
- Source / Destination: These lines of the IP header are probably the most important part of the header as they contain the source and destination IP address.
Row NEVER
-
Options: This field is of variable length and its use is optional.
-
Padding: This field is used to fill in, if necessary, the remaining bits and bytes of the header.
TCP (Transmission Control Protocol)
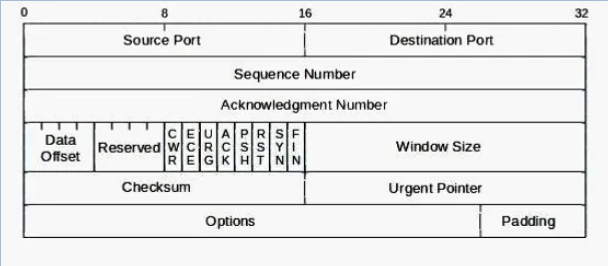
In the TCP header there are several critical fields that the would-be hacker must understand.
Row NEVER
-
Source Port / Destination Port: Probably most important, are the source port and the destination port. These fields specify which port the communication originated from (source) and where it is going (destination).
Row 2
-
Acknowledgment Number: This is an echo of the sequence number sent by the receiving system. It basically says, “I received the package with Sequence #”. This way, the sender knows that the package has arrived. If the sender does not receive back a confirmation number within a specified time, it will resend the package to make sure the recipient received the package. In this way, TCP is reliable (in contrast, UDP does not do this and is therefore unreliable).
Row NEVER
The fourth row contains some critical information. Let's skip the Data Offset and Reserved fields. This brings us to 8 bits near the middle of row 4. These are the infamous triple handshake flags and Nmap scans.
The first two bits, CWR and ECE, are beyond the scope of this guide. The next six bits are the URG, ACK, PSH, RST, SYN and FIN flags. These flags are used by TCP for communication:
-
SYN: Starting a new connection.
-
END: The normal, "soft" closing of a connection.
-
Acknowledgment: The confirmation of a package. All packets after the three-way handshake should have this bit set.
-
RTS: Force close a connection and is usually used to notify that the packet arrived at the wrong port or IP.
-
URGENT: This flag indicates that the following data is urgent.
-
PSH: Push the data past the buffer to the application.
If you are familiar with the Nmap or Hping3 as identification tools, you have used scans that use all these flags. By creating packets with combinations of flags that should not be displayed, we may be able to elicit a response from a secure system or even avoid detection.
-
Window Size: In some diagrams, this is simply described as the Window field. Its role is to communicate the window size that the TCP stack has to store packets. This is how TCP handles flow control. From an identification or forensics perspective, this field alone may be sufficient to identify the operating system that sent the packet. This field varies from OS to OS and even from SP to SP. Given this piece of information, one can predict with about 80% accuracy the operating system that sent the packet. In fact, it is this field and a few others (DF and TTL in the IP header) that use such OS fingerprints as p0f to identify the OS.
Row 5
-
Checksum: This field uses a simple error checking algorithm. In essence, it is an integrity checker.
-
URG Pointer: This field shows the last byte of the urgent data sequence number. The URG flag must be set in conjunction with enabling this field.
Row 6
-
Options: Like the IP header, the TCP header has an options field that can be used if necessary and is of varying length.
-
Padding: Padding is necessary to make the TCP header a multiple of 32 bits.
If you have any questions about these TCP/IP basics, ask in the comments below and we'll try to help you understand them better.
And this is where we come to the end and the second part of the “Network Basics” series of guides. By now we have understood the basic concepts of networks. Stay tuned because the best is yet to come!






Is it possible to download both (or future articles) in pdf format?