When WannaCry hit around the world in mid-May, it has been reported many times that extensive use of the old Windows XP operating system has helped spread the infection very quickly.
Η Εθνική Υπηρεσία Υγείας του Ηνωμένου Βασιλείου ήταν ένα από τα θύματα της επίθεσης με τα υψηλότερο προφίλ - και πολλά από τα εξατομικευμένα συστήματά της εξακολουθούν να χρησιμοποιούν Windows XP. Η Microsoft αν θυμάστε έσπευσε να κυκλοφορήσει μια ενημερωμένη έκδοση ασφαλείας για το μακροχρόνια μη υποστηριζόμενο functional system.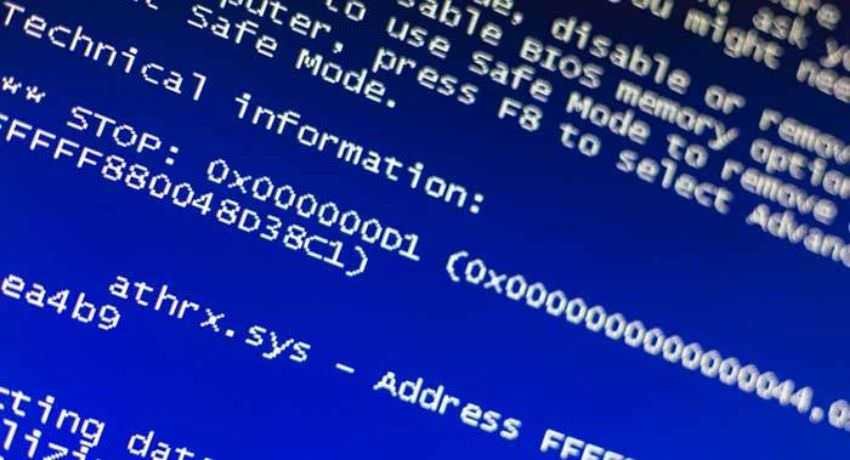
And while Windows XP systems were among those hit by WannaCry, later an analysis showed that 98 percent of the victims used Windows 7.
Αλλά αυτό δεν σημαίνει ότι το WannaCry δεν λειτούργησε για τους στόχους που χρησιμοποιούσαν τα Windows XP. Σύμφωνα με μια νέα αναφορά ερευνητών της Kryptos, ενώ το συγκεκριμένο λειτουργικό σύστημα ήταν ως επί το πλείστον το πιο επικίνδυνο για να πέσει θύμα του ransomware, πολλές επιθέσεις οδήγησαν απλά σε συντριβή συστημάτων και την εμφάνιση της "μπλε οθόνης του θανάτου." Μετά από αυτό χρειαζόταν επαναφορά του συστήματος.
The researchers looked at WannaCry's ransomware in some operating systems in a test environment: Windows XP with Service Pack 2, Windows XP with Service Pack 3, Windows 7 x64bit with Service Pack 1, and Windows Server 2008 Service Pack 1.
While Windows 7 attacks successfully installed WannaCry, after many attempts, supposedly vulnerable Windows XP was much more resistant to ransomware than expected, and the operating system running the 2 Service Pack was not infected at all.
However Windows XP with SP 2 was affected, but instead of being infected with WannaCry and demanding a ransom in exchange for the locked files, the system displayed the blue screen of death (blue-screen of death) and were constantly restarting.
The phenomenon was undoubtedly disappointing for organizations that found their systems to make continuous restarts but at least were not infected by ransomware.
This does not mean that Windows XP is not vulnerable, as this operating system remains a popular target for cyber criminals who are trying to exploit the weaknesses of unaware systems.
WannaCry caused chaos across the globe, and the identity of the attackers remains unknown. Security companies such as Symantec and Kaspersky have linked the attack with the Lazarus team, which is believed to have acted for North Korea.
Meanwhile, the linguistic analysis of the ransom notes appearing on his victims maliciousy software suggests that the author or at least the one who wrote the ransom note was Chinese.





