When WannaCry hit around the world in mid-May, it has been reported many times that extensive use of the old Windows XP operating system has helped spread the infection very quickly.
The UK National Health Service has been one of the victims of the high-profile attack - and many of its personalized systems still use Windows XP. Microsoft, if you remember, hastened to release a security update for the long-standing unsupported operating system.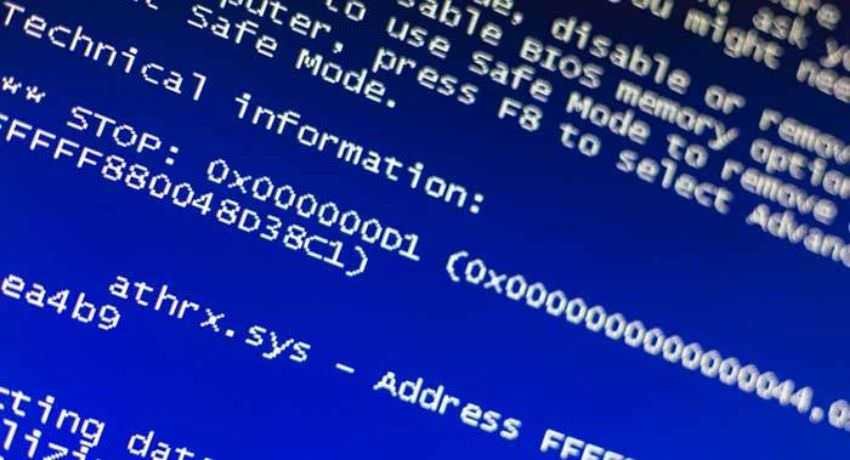
And while Windows XP systems were among those hit by WannaCry, later an analysis showed that 98 percent of the victims used Windows 7.
But that doesn't mean WannaCry didn't work for targets running Windows XP. According to a new report from Kryptos researchers, while this particular operating system was mostly the most dangerous to fall victim to ransomware, many attacks simply resulted in system crashes and the appearance of the "blue screen of death." After that it was needed reset of the system.
Researchers tested WannaCry ransomware on some operating systems in a test environment: Windows XP with Service Pack 2, Windows XP with Service Pack 3, Windows 7 x64bit with Service Pack 1, and Windows Server 2008 with Service Pack 1.
While Windows 7 attacks successfully installed WannaCry, after many attempts, supposedly vulnerable Windows XP was much more resistant to ransomware than expected, and the operating system running the 2 Service Pack was not infected at all.
However, Windows XP with SP 2 was affected, but instead of being infected with WannaCry and asking for a ransom in exchange for locked files, the system displayed a blue-screen of death and repeated reboots.
The phenomenon was undoubtedly disappointing for organizations that found their systems to make continuous restarts but at least were not infected by ransomware.
This does not mean that Windows XP is not vulnerable, as this operating system remains a popular target for cyber criminals who are trying to exploit the weaknesses of unaware systems.
WannaCry wreaked havoc across the globe, and the identity of the attackers remains unknown. Security companies such as Symantec and Kaspersky, have linked the attack to the group Lazarus, believed to have acted for North Korea.
Meanwhile, the linguistic analysis of ransom notes that appeared to victims of malware suggests that the writer or at least the one who wrote the ransom note was Chinese.





