The concept of password has existed for centuries and passwords applied to information technology much earlier than most of us can remember.
One reason for the popularity of passwords is that people instinctively know how they work. But there is a problem. The passwords are Achilles' heel of the digital lives of many people, especially as we live in an age where the average person can remember 100 login codes, with this number increasing in recent years.
"It is not surprising that many people choose easy solutions, resulting in reduced security" he says Phil Muncaster, by the cybersecurity company team ESET.
Since the Password is often the only obstacle που στέκεται ανάμεσα σε έναν κυβερνοεγκληματία και τα προσωπικά και οικονομικά σας δεδομένα, οι απατεώνες είναι περισσότερο από πρόθυμοι να κλέψουν ή να σπάσουν αυτούς τους codeς. Εναπόκειται σε εμάς να προστατεύσουμε τους διαδικτυακούς λογαριασμούς μας.
What can a hacker do if he gets my password?
Passwords are the virtual keys for your digital world - offer access to your online banking, email, social networking services, accounts Netflix and Uber and all data hosted in the cloud.
With your passwords in his hands, a hacker could:
- To steal your personal information and to sell them to other criminals.
- To sell passwords. Dark web sites market this information roughly. Unconscious buyers could use passwords to get everything, from free taxi rides and streaming services, to discount travel on Air Miles pirate accounts.
- Use passwords to unlock other accounts in which you use the same password.
How do hackers steal passwords?
Phil Muncaster, from the team at cybersecurity company ESET, suggests that we familiarize ourselves with these classic cybercrime techniques to be able to manage the threat:
- Phishing and social engineering
Human beings are prone to error when making hasty decisions. Cybercriminals exploit this weakness through the social engineering, a psychological trick designed to push us to do something we should not do. The electronic fishing (phishing) is perhaps the most representative example. Here, the hackers disguised as friends, relatives, companies with which you have collaborated etc. The email or text you will receive will look authentic, but will include one malicious link ή attached file, which if clicked will download malware or will take you to a web page to fill in your personal information.
Fortunately, there are many ways to detect the warning signs of a phishing attack, as we explain here. Scammers use even phone calls to extract passwords and other personal information directly from their victims, often pretending to be technical support representatives. This method is called "vishing”(Voice phishing).
- Malware / Malware
Another popular way to get your passwords is malware. Fishing emails are the primary vehicle for this type of attack, although you may fall victim to them. by clicking on a malicious ad on the internet (malvertising) or if you visit a violated website (drive-by-download). As the ESET researcher has shown many times Lukas Stefanko, malware can even hide in a mobile app that looks legal, which is often found in third-party application stores.
There are various types of malware that steal information, but some of the most common ones are designed to record typing or take snapshots of your device screen and send them to attackers.
- Attacks Brute forcing
Ο number of passwords that the average person should manage increased by approx 25% on an annual basis in 2020. Many people use passwords that are easy for someone to remember (and guess) and use them on many different websites. However, this can open the door to so-called techniques brute-strength.
One of the most common are those of the press credential stuffing. Here, attackers feed into automated software large volumes of username / password combinations that have been compromised in the past. The tool then tests these combinations on a large number of websites, hoping to find a match. In this way, hackers can unlock many of your accounts with a single password. According to an estimate, Last year, some 193 billion such efforts were made worldwide. The Government of Canada was one of the victims of this technique.
Another technique brute-force is the type attack password spraying. In that case hackers use automated software to try a list of frequently used passwords in your account.
- Guessing
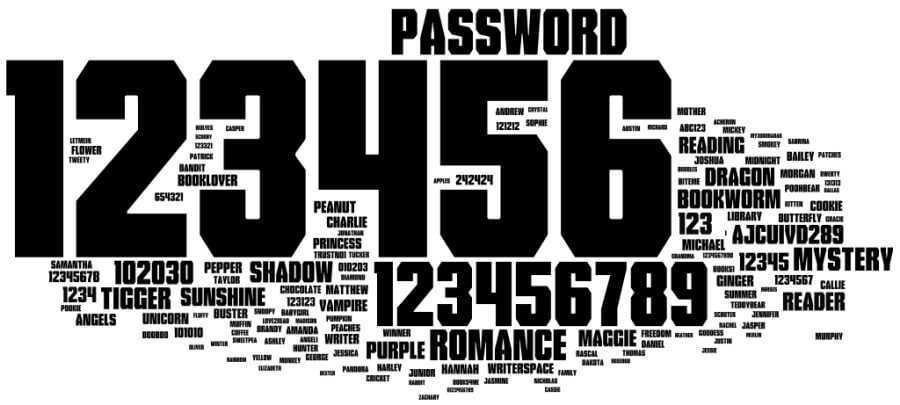
Although hackers have automated tools for hacking your password, sometimes they are not even necessary: even the simple conjecture - in contrast to the more systematic approach used in Brute Force attacks - can do the job. The most common password of 2020 was the "123456" followed by "123456789". In 4th place was the word…"Password".
And if you're like most people and you use the same password, or a derivative thereof on multiple accounts, then make it even easier for scammers and you put yourself at extra risk identity theft and scams.
- Shoulder surfing - Peeking over the victim's shoulder
All the password breach paths we have explored so far have been virtual. However, as quarantine loosens and many employees begin to return to the office, it is worth remembering that some tried and tested eavesdropping techniques are also a risk. That's not the only reason why shoulder surfing is still a danger, and Jake Moore ESET recently conducted an experiment to see how easy nviolate someone's Snapchat using this simple technique that assumes the physical presence of the attacker close to the victim user so that the former has eye contact and can see the keyboard and screen of the latter.
A higher tech version, known as an attack "Mon-in-the-middle" which includes Wi-Fi spying, can allow hackers who are connected to public Wi-Fi networks monitor your password as you enter it while logged in to the same node. Both techniques have been around for years, but that does not mean they are not yet a threat.
How to protect the login credentials of your accounts
You can do a lot to block these techniques - by adding a second form of authentication, managing your passwords more effectively, or taking steps to prevent theft in the first place.
Consider the following:
- You use only strong and unique passwords ή access phrases all of your online accounts, especially your bank accounts, email accounts, and social media accounts.
- Do not use the same password in different accounts.
- Turn it on two-factor authentication (2FA) on all your accounts.
- Use one password manager, which will store strong, unique passwords for each website and each account, making connections simple and secure.
- Change your password immediately if a Provider notifies you that your data may have been compromised.
- To visit only websites https: //
- Do not click in links and do not open attachments in spam emails
- You download applications only from official app stores
- Invest in security software by one reliable provider for all your devices
- Make sure all operating systems and applications are upgraded in the latest version
- Beware of poachers (shoulder surfers) in public places
- Never connect in an account if you are on a public network Wi-Fi. If you must use such a network, use a VPN.
Secure access to accounts with methods that do not involve the use of a password has been studied for over a decade. However, the alternatives can not yet replace the password, which means that users need to take matters into their own hands. Stay alert and keep your login data secure.





